eDOT Solutions is committed to provide consultancy, as well as dynamic cyber security management services to ship managers, owners and operators. Having successfully merged the shipping and the IT sectors, eDOT understands the seafaring mindsets, thus providing real-time value propositions rather than getting lost in over information bombardment.
Ship Cyber Security
Solutions from certified ISO 27001 lead auditors
Consulting Overview
-
Technology has overtaken our capacity for keeping up with it.
- Regulations & standards are trailing behind technological & commercial development.
- Ships are increasingly using systems that rely on digitization, integration, and automation - As a result, security of data and other sensitive information has become a major concern – operations have become vulnerable !!
-
The industry is challenged from the continued reliance on legacy systems – an assumption of insulation from cyber threats..
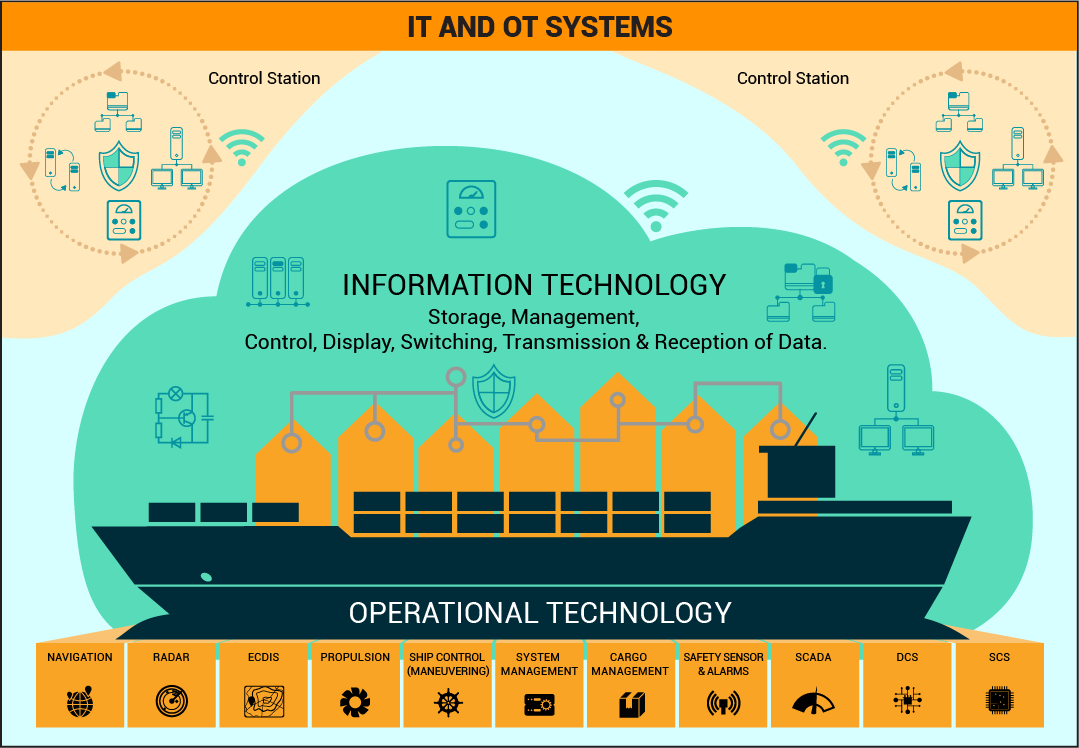
- Understanding of IT & OT systems!!! Special ref to operating systems – radars, radios.
- If your organization is in need of cyber security professionals, we are here to assist.
- Our security consultants can be available on demand, or full time to meet operational challenges.

Cyber Security & Ships
Do we understand | Are we preparing | Can we sustain
With widely reported cyber-attacks on network of mega shipping companies like Maersk & Anglo Eastern cyber security awareness & the run to compliance is gaining momentum.
The Maritime industry has been overtaken by technology, & while we are struggling to come to terms with it,
cyber-attacks on maritime infrastructure are gaining critical momentum. In this article, I have tried to simplify the identification some of vulnerabilities existing onboard merchant ships, analyse them and look at the road ahead.
The writer is the CEO of eDOT solutions, Which designs, implements & manages Cyber Security Solutions for ship owners & managers.
 Download a digital copy of published article
Download a digital copy of published article
What we want to do !!!

Develop Culture
-
Develop a cybersecurity culture amongst the ships’ officers & crew
Policies Updates
-
Organise and prioritise existing policies for cybersecurity
Policy Implementation
-
Develop and plan the implementation of new relevant policies
Daily Operations
-
Organize the day to day software and hardware management onboard ships in a controlled manner
Utility Standarisation
-
Standardise the hardware and software utilities over a period of time
Protocols
-
Ensure that third party vendors are using best possible protocols to mitigate posed risks
-
Periodically review the cybersecurity policy given the ever increasing security threats with emerging technologies
Controls
-
Put you in control with satisfaction & confidence
Network Rationalisation
-
Map & prepare physical and logical network plans
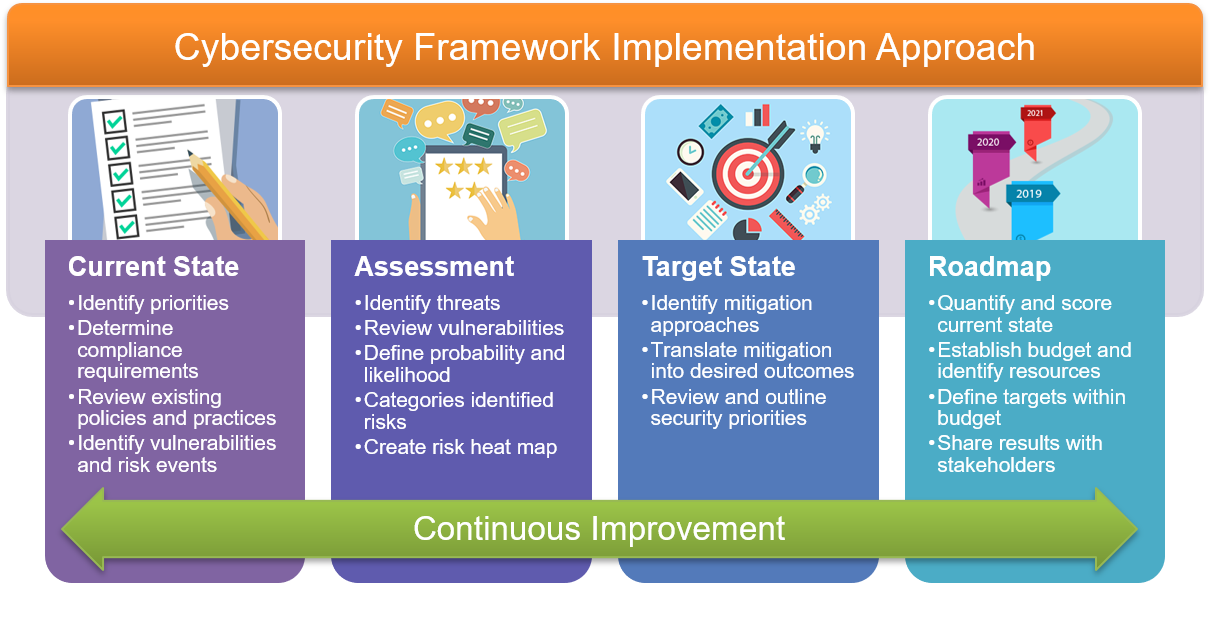
Cyber Security Framework
Consulting Areas

Firewall Consultants

Intrusion Prevention Consultants

Network Access Control (NAC) Security Consultants

Vulnerabilty Scanning Consultants

Cyber Security Project Managers

Vendor Risk Management Consultants

Penetration Testing Consultants

Vulnerability Management Consultants

Web Application Security Consultants

Cyber Incident Investigation Consultants
Compliance Experts

GDPR Consultants
Outcomes
Compliance with IMO RES 428, Class Certification VIQ7 & even 27001:2013 Certification would be achieved organically without any added effort or stress
 Download our Cyber Security Whitepaper
Download our Cyber Security Whitepaper
It is relevant to note that understanding the concept of “operational technology – (OT)”, and its differences from ‘information technology (IT)”, is essential for estimating potential impact to operations and safety of the vessel.
These concepts are explained in my papers published earlier.
 Download our OT Risk Assessment Whitepaper
Download our OT Risk Assessment Whitepaper
In recent times, the approach of the industry has been very subjective and diverse about OT near-miss reporting. This paper attempts to create a focused line of thought in identifying & reporting of Cyber Security related OT near-misses. In a small way, I hope it will help ship managers, as well as the sailing staff, in getting familiarized with the requirements of a Cyber Security Management System.
 Download our OT Near Miss Whitepaper
Download our OT Near Miss Whitepaper
Recognizing, reporting and recording of IT near-miss & incidents is an integral part of the process, and is expected to go a long way in experiential learning of the seafarers, as well as educating the shore IT support staff about shipboard experiences and how to make the change in vocabulary & instruction-documents for better understanding of the seafarer.